What is TTP – Tactics, Techniques, and Procedures – in Cyber Security?
Stay Informed With Our Weekly Newsletter
Receive crucial updates on the ever-evolving landscape of technology and innovation.
In the ever-evolving realm of cybersecurity, TTP – Tactics, Techniques, and Procedures – has become a cornerstone.
These are the patterns of activities or methods associated with a specific threat actor or group of threat actors.
Understanding TTPs is crucial for both defensive and offensive cyber operations.
Key resources include organisations like the Open Web Application Security Project (OWASP) and the Cyber Threat Alliance (CTA).
This comprehensive guide will delve into the intricacies of TTPs in cyber security, shedding light on their importance, how they are identified, and how they can be used to enhance cyber security strategies.
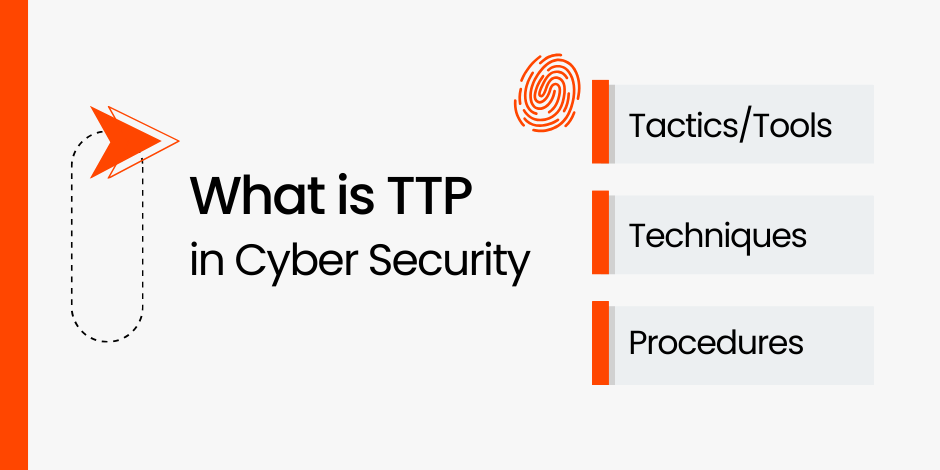
Defining tactics, techniques, and procedures

The term tactics, techniques, and procedures is borrowed from the military, where it is used to describe the methods used by an adversary in warfare.
In the context of cyber security, TTPs refer to the patterns of activities or methods associated with a specific threat actor or group of threat actors.
Tactics
Tactics in cyber security refer to the overarching objectives or strategic goals of the threat actor. These could include goals such as data theft, system disruption, or financial gain.
Techniques
Techniques, on the other hand, refer to the ‘how’ of a cyber attack. These are the methods or tools used by the threat actor to achieve their tactical goals.
Techniques in cyber security can range from phishing attacks and malware distribution to advanced persistent threats (APTs) and zero-day exploits.
Procedures
Procedures are the specific steps taken by the threat actor using the chosen techniques.
These are the granular details of the attack, providing insight into the exact actions taken by the threat actor at each stage of the attack lifecycle.
Procedures can include steps such as initial system reconnaissance, exploitation of vulnerabilities, and data exfiltration.
The importance of understanding TTPs in cybersecurity
Understanding tactics, techniques, and procedures in cyber security is crucial for several reasons.
Firstly, it provides insight into the threat landscape, helping to identify the most prevalent threats and the tactics, techniques, and procedures used by threat actors.
Secondly, understanding TTPs can aid in threat attribution. By analysing the tactics, techniques, and procedures used in a cyber attack, it may be possible to identify the threat actor or group responsible.
Informing cyber security strategies
One of the primary benefits of understanding tactics, techniques, and procedures in cyber security is their ability to inform and enhance cyber security strategies.
This can involve implementing specific countermeasures to mitigate the techniques used by threat actors or adjusting security policies to address the tactics identified.
Aiding in threat attribution
Understanding tactics, techniques, and procedures can also aid in threat attribution.
By analysing the tactics, techniques, and procedures used in a cyber attack, it may be possible to identify the threat actor or group responsible.
This can be particularly useful in the context of nation-state cyber attacks, where attribution can have significant geopolitical implications.
Identifying TTPs in cyber security
Identifying TTPs in cyber security involves a combination of threat intelligence, incident response, and forensic analysis.
Once identified, TTPs can be catalogued and shared with other organisations to enhance collective cyber security efforts.
This is often done through threat intelligence sharing platforms or through industry-specific Information Sharing and Analysis Centres (ISACs).
Developing incident response plans
Understanding TTPs can also aid in the development of incident response plans.
By knowing the tactics, techniques, and procedures that a threat actor is likely to use, organisations can develop response plans that are tailored to these specific threats.
This can help to reduce the impact of a cyber attack and speed up the recovery process.
In conclusion
Understanding tactics, techniques, and procedures in cyber security is crucial for any organisation looking to enhance its cyber defences.
To deepen your knowledge of tactics, techniques, and procedures in cyber security and effectively bolster your defence strategies, consider exploring the Institute of Data’s specialised cyber security program.
Alternatively, don’t hesitate to schedule a complimentary career consultation with our team of experts to discuss your options.